Whoever Satoshi Nakamoto is or was, the author's 2008 paper on blockchain technology is now regarded as one of the most important developments in computer science this century. As the blockchain is increasingly used as a platform for building cryptocurrencies like Bitcoin and Ethereum, more and more researchers are getting involved in the science behind the cryptography that's driving it – including in Ireland.
That’s because developments in cryptography have made the blockchain what it is today: a secure system for making transactions across an open distributed ledger. The cryptography behind it is a kind of public key technology, which was first invented in the 1970s, and provides a fast and efficient way for many people to use encryption at the same time, and communicate securely with each other.
Prof Gary McGuire, at UCD School of Mathematics and Statistics leads a research group working on the topic. "Blockchain technology uses a type of public-key cryptography known as elliptic curve cryptography," he says, "which uses the complicated arithmetic operations that can be done on an elliptic curve to obtain security."
Elliptic curve cryptography was invented in the 1980s, and provides a way for each user to digitally sign a document. “This is known as ECDSA – Elliptic Curve Digital Signature Algorithm,” McGuire explains, “and is what blockchain uses when each transaction is recorded in the ledger.”
Unbreakable
The mathematics involved in elliptic curve cryptography is quite advanced, meaning that to break it and crack the code, one has to reverse engineer some complicated maths.
According to McGuire, like all cryptographic systems, there is no mathematical proof of security, but there is a general belief that this form of cryptography is secure because experts who have tried to break it have failed.
“So far nobody has been able to break it,” he says, “and it’s believed by the community who work on these things that elliptic curve cryptography will not be broken.
“My research group studies the mathematics underlying this type of cryptography, including ways of potentially cracking it,” he says. “When it comes to breaking elliptic curve cryptography, lots of people have tried lots of clever ideas, but nothing has worked.”
However, McGuire says that elliptic curve cryptography would not remain secure if quantum computing eventually became a realisation. That would mean a different digital signature scheme to ECDSA would have to be used in the future, and in the coming years it is very likely that people will propose new blockchain systems with different digital signature schemes.
Quantum future
That’s where work on cryptographic techniques done at Queen’s University Belfast may take the lead. Prof Máire O’Neill, at the Centre for Secure Information Technologies (CSIT), Queen’s University Belfast, is currently conducting research in security which looks at quantum-resistant cryptography.
According to O’Neill, the realisation of quantum computers is ever closer and some researchers are predicting their availability within the next decade. “Since quantum computing offers dramatic speed-up over classical computing,” she says, “when it becomes a reality, commonly used public-key security algorithms that are used to provide security in all of today’s communications systems – like the internet and e-commerce – will be broken.”
Because of this apparent inevitability, a lot of research effort is now being focussed on post-quantum, or quantum-safe, cryptography. This kind of cryptography refers to conventional non-quantum security algorithms that are secure today, and should remain secure even after practical quantum computing becomes a reality, O’Neill adds.
“Block chain technology uses hash functions that are used to ensure the integrity of previous blocks,” she says. “A hash function is a form of symmetric key cryptography – where the same key is used to encrypt and decrypt a message – and it is believed that this form of cryptography will be secure against quantum attacks if the key sizes used in the hash functions are doubled.”
“So, the focus of our research is on public-key cryptography, where a pair of different keys, a public and a private key, is used in the encryption-decryption process.”
So far, O’Neill and her colleagues have developed an open-source library of quantum-safe algorithms, and have illustrated the use of their research in satellite communications. They have also shown that quantum-safe solutions are as efficient as the solutions in existence today.
“In the near future,” she says, “all current communications systems will need to upgrade to quantum-safe security.”
Conor Purcell is a science journalist with a PhD in Earth Science. Twitter: @ConorPPurcell – some of his other articles are at cppurcell.tumblr.com
Panel: Elliptic curve cryptography
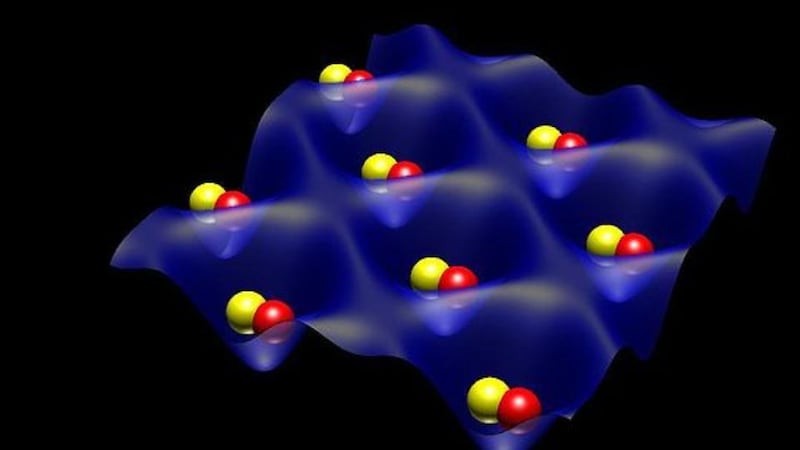
Elliptic curve cryptography is a kind of public-key cryptography which is based on the mathematical structure of elliptic curves over finite fields. The complex mathematics of elliptic curves has turned out to be rather useful, and has become applicable for encryption, pseudo-random generators and digital signatures.
“Each instance of elliptic curve cryptography actually involves a choice of certain input numbers,” says Prof Gary McGuire, at UCD School of Mathematics and Statistics. “For example, Whatsapp encryption uses a particular elliptic curve known as Curve25519. Bitcoin uses an elliptic curve called secp256k1.”
“We try to find particular instances of numbers where the cryptography may be weak, which warns users not to use them. But it still means that it’s secure for other choices of numbers.”
McGuire’s team also work on instances of elliptic curve cryptography that are secure, but where algorithms can make improvements by increasing their speed. This is important in applications where calculations have to be performed in real time.
“The blockchain is one day going to be so large that the signatures will take too long to be calculated,” he says, “at which point the system breaks down.”










