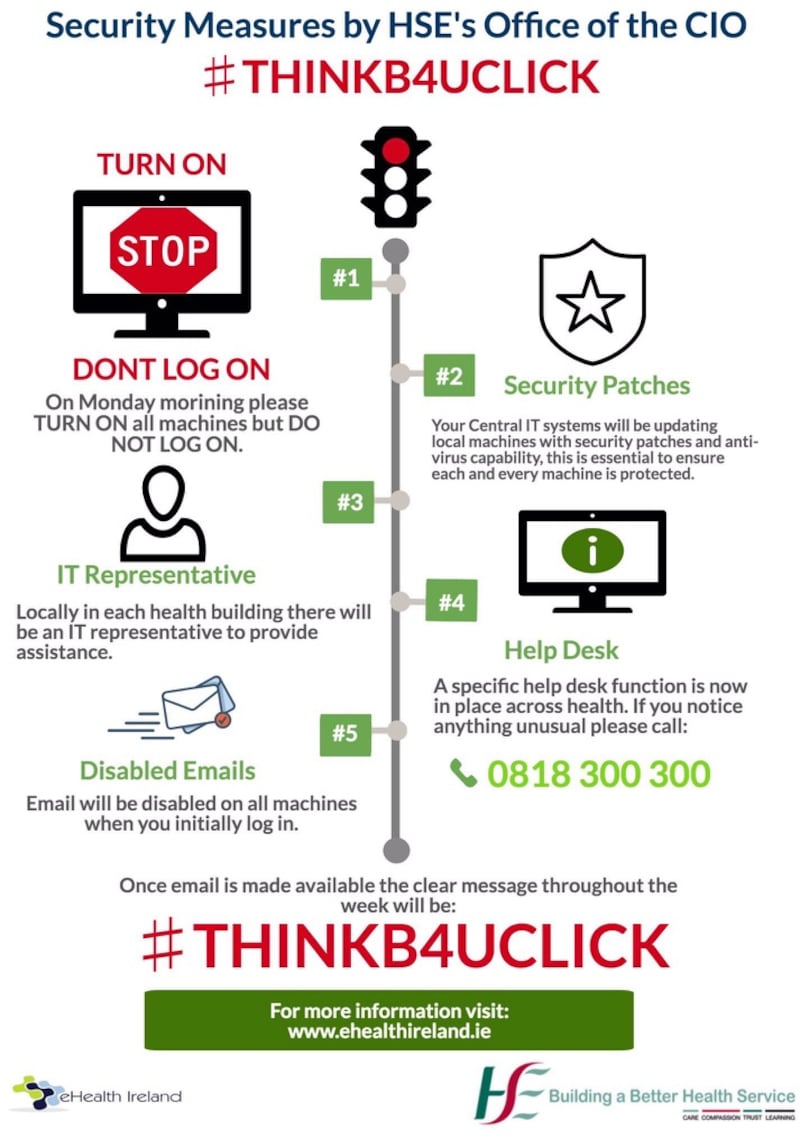
All Health Service Executive staff are being asked to switch on computers on Monday morning but not to log on, in the wake of the global ransomware attack over the weekend.
Switching on will allow the HSE’s central IT systems to update local machines with security patches and anti-virus capability, it said.
When it is eventually possible to log in after the screening process, emails will not initially be accessible, the service told staff. It added: “Once email is available the clear message throughout the week will be: #THINK B4UCLICK.”
This is a reminder for employees not to click on suspect attachments or attachments from email addresses they are not familiar with.
An IT representative will be available in all health service buildings to provide assistance.
The HSE also confirmed a section 39 agency in Co Wexford was affected by the cyber attack.
The extent of the damage at the State-funded agency is not yet known. It has been isolated and work will begin on Monday on repairs.
It affected a small number of machines, which will be removed tomorrow and the data will never be recovered.
Business group Ibec called for fresh funding to tackle ransomware threats, saying it was liaising with the Department of Communications to monitor the situation.
“Ibec has previously called for adequate resourcing of the National Cyber Security Centre and the implementation of a cyber security programme. Government provided extra funding in this regard to the Department of Communications, Climate Action and Environment in Budget 2017 and in view of the increased threat we call for this funding to be increased significantly further,” said Erik O’Donovan, Ibec’s head of digital policy.
The Garda had said early on Sunday there was no identified cyber attack on any Irish State computer system from the wave of international ransomware attacks.
Scrambling to patch computers
Meanwhile, technical staff in scores of businesses and government agencies across the globe were scrambling on Sunday to patch computers and restore infected ones, amid fears that the ransomware worm that stopped car factories, hospitals, shops and schools could wreak fresh havoc on Monday when employees log back on.
Cybersecurity experts said the spread of the virus dubbed WannaCry - “ransomware“ which locked up tens of thousands of computers - had slowed, but the respite might only be brief.
New versions of the worm are expected, they said, and the extent of the damage from Friday’s attack remains unclear.
The head of the European Union's police agency Europol said on Sunday that the cyber attack had hit 200,000 victims in at least 150 countries and that number could grow when people return to work on Monday,
Europol director Rob Wainwright told ITV's Peston on Sunday programme the attack was unique in that the ransomware was used in combination with "a worm functionality" so the infection spread automatically.
“The global reach is unprecedented. The latest count is over 200,000 victims in at least 150 countries, and those victims, many of those will be businesses, including large corporations,” he said.
Monday warning
“At the moment, we are in the face of an escalating threat. The numbers are going up; I am worried about how the numbers will continue to grow when people go to work and turn (on) their machines on Monday morning.”
He said Europol and other agencies did not yet know who was behind the attack but “normally it is criminally minded and that is our first working theory for obvious reasons”.

“Of course there are amounts that are being demanded, in this case relatively small amounts - $300 rising to $600 if you don’t pay within three days,” he said.
“[There have been] remarkably few payments so far that we’ve noticed as we are tracking this, so most people are not paying this, so there isn’t a lot of money being made by criminal organisations so far.”
Mr Wainwright said Europol had been concerned about cyber security in the healthcare sector, which deals with a lot of sensitive data, but declined to comment on whether Britain’s National Health Service had been adequately funded.
Defence minister Michael Fallon told the BBC the British government under prime minister Theresa May was spending around £50 million (€58.9 million) on improving computer systems in the NHS after warning the service that it needed to reduce its exposure to "the weakest system, the Windows XP".
"The NHS was not particularly targeted. There were the same attacks applied to Nissan on Friday and in other areas of the economy and indeed around the world," Fallon said.
“But let me just assure you, we are spending money on strengthening the cyber defence of our hospital system.”
Additional reporting: Reuters









